The digital threat landscape is a 24/7 battleground. Cybersecurity professionals are constantly working to identify and neutralize threats before they can wreak havoc. One such threat, the XRed backdoor masquerading as the legitimate Synaptics.exe process, has been identified and analyzed. This article delves into the intricacies of this backdoor, its delivery mechanisms, persistence techniques, and provides crucial recommendations for mitigating its potential impact.
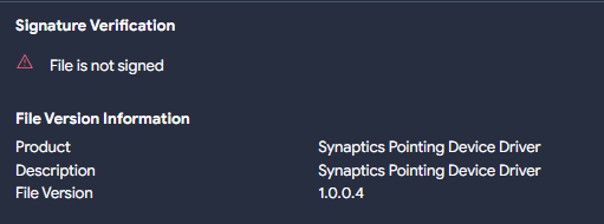
While the legitimate synaptics.exe is a critical component for touchpad functionality on many devices, the malicious variant identified by eSentire’s Threat Response Unit (TRU) serves a far more sinister purpose. This backdoor, dubbed “XRed”, has been active since at least 2019 and poses a significant threat to unsuspecting users.
Dissecting the XRed Infection Chain
The initial infection vector for XRed involves a trojanized version of “Windows InstantView.exe,” a legitimate application associated with certain USB docks. This malicious executable mimics the behavior of the genuine software, downloading and running it as a decoy while simultaneously deploying the synaptics.exe payload to the system.
The malicious synaptics.exe file is strategically placed within a hidden folder under C:ProgramDataSynaptics and its persistence is ensured through a registry run key. This allows the backdoor to launch automatically each time the system starts.
XRed’s Arsenal of Malicious Capabilities
Beyond persistence, XRed boasts a range of functionalities designed to compromise the infected system. It can collect sensitive information such as MAC addresses, usernames, and computer names, transmitting this data to the attacker via email.
Keylogging capabilities, achieved through keyboard hooking, allow the backdoor to capture every keystroke made by the user, potentially exposing passwords and other confidential data. Furthermore, XRed can execute remote commands, providing the attacker with significant control over the compromised machine.
This backdoor also exhibits worm-like behavior, propagating itself through USB drives by creating autorun.inf files. This facilitates automatic execution of the malware when the infected drive is inserted into another system. An embedded password-protected VBA script further enhances XRed’s capabilities, allowing it to inject malicious code into existing XLSM files and disable security warnings.
Mitigating the XRed Threat
Protecting against sophisticated threats like XRed requires a multi-layered approach. Implementing robust security measures, such as regularly updating antivirus software, disabling macros with notifications, and educating users about the risks associated with USB drives and suspicious files are crucial. Regular system audits and security awareness training are essential for early detection and prompt response to potential threats.
Conclusion
The XRed backdoor, disguised as the innocuous synaptics.exe, exemplifies the constant evolution of cyber threats. Understanding its infection vectors, persistence mechanisms, and malicious capabilities is paramount for effective mitigation. By adopting proactive security measures and fostering a culture of security awareness, individuals and organizations can significantly reduce their risk of falling victim to this insidious threat. For a comprehensive list of Indicators of Compromise (IOCs) and detection rules, please refer to the resources provided by eSentire’s Threat Intelligence team.